News-driven stories and thought-leadership pieces require a different approach than marketing content, because the implicit CTA at the end isn't "act now"; it's "trust us."
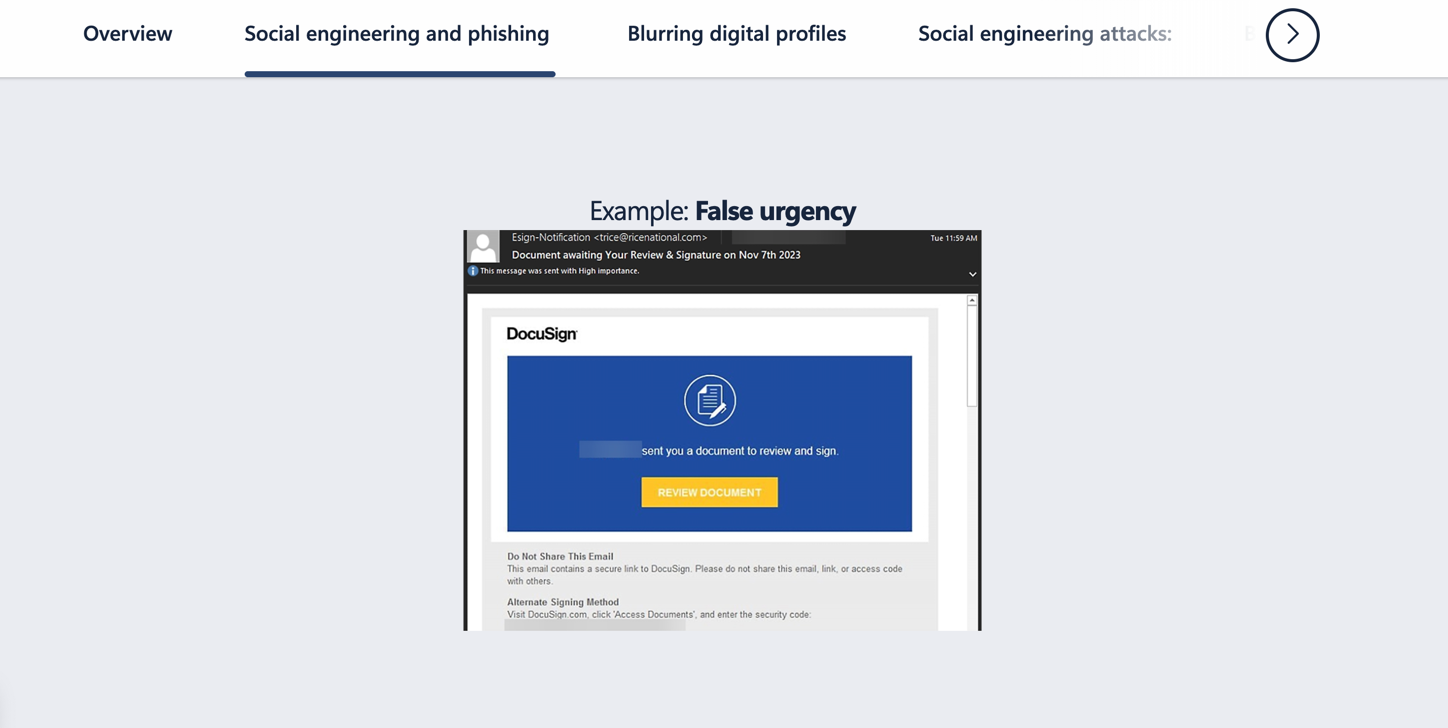
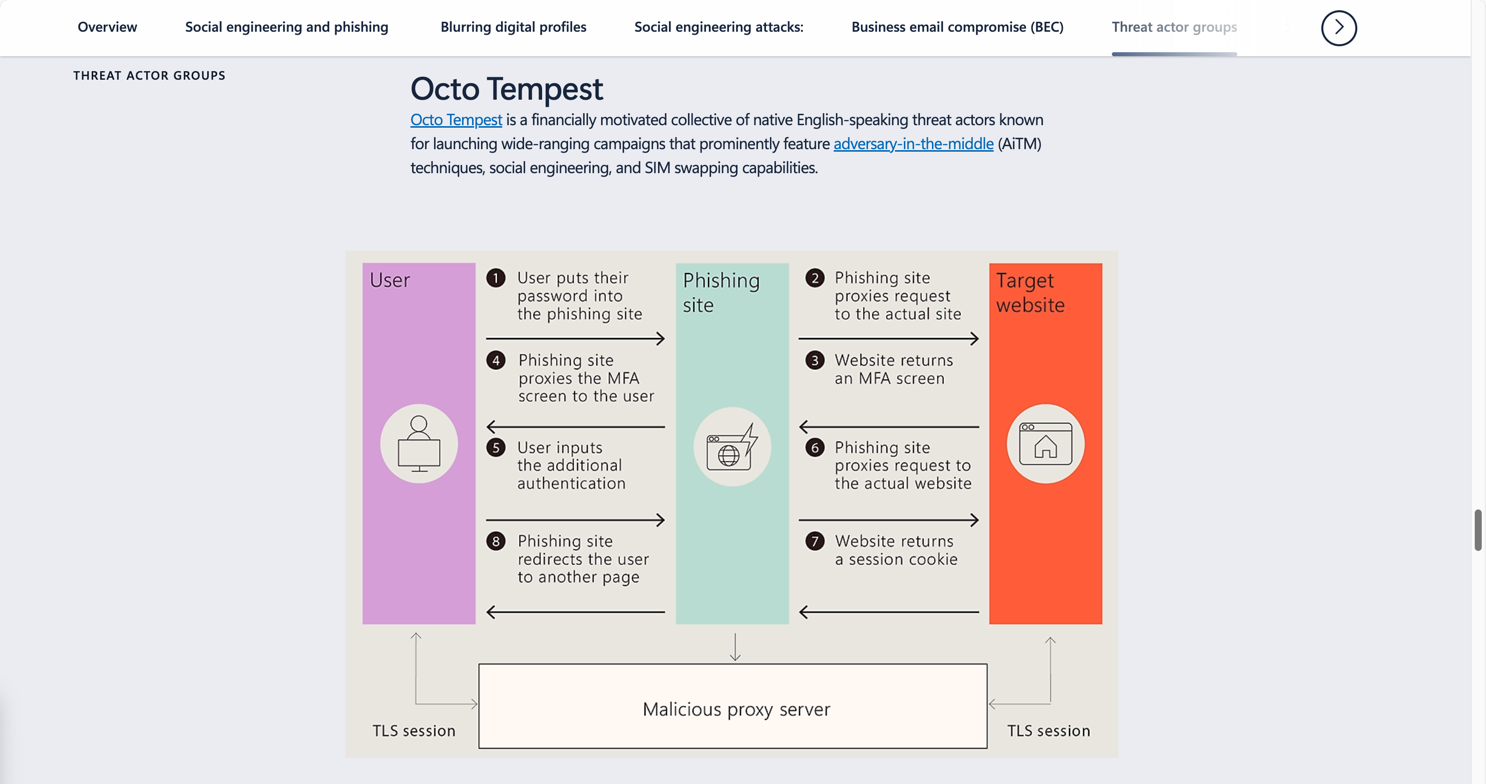
Feeding from the Trust Economy: Social Engineering Fraud
The Ask: Go beyond simple "don't get phished" advice and explain the sophisticated psychological tactics that make modern social engineering so effective.
My Role: I converted transcripts from threat intelligence experts into a compelling journalistic narrative, focusing on the "why" behind the scams to build true audience understanding.
The Outcome: An anchor editorial feature for Microsoft's Security Insider that provides a deep dive into the human element of modern cyber threats.
Read feature story
Read feature story

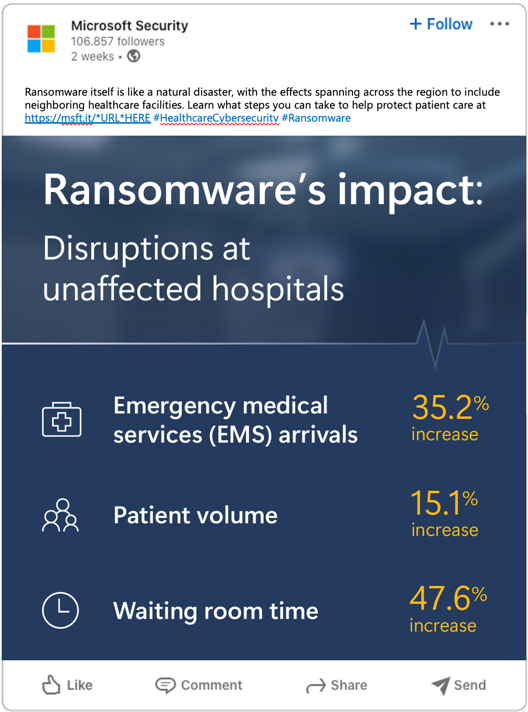
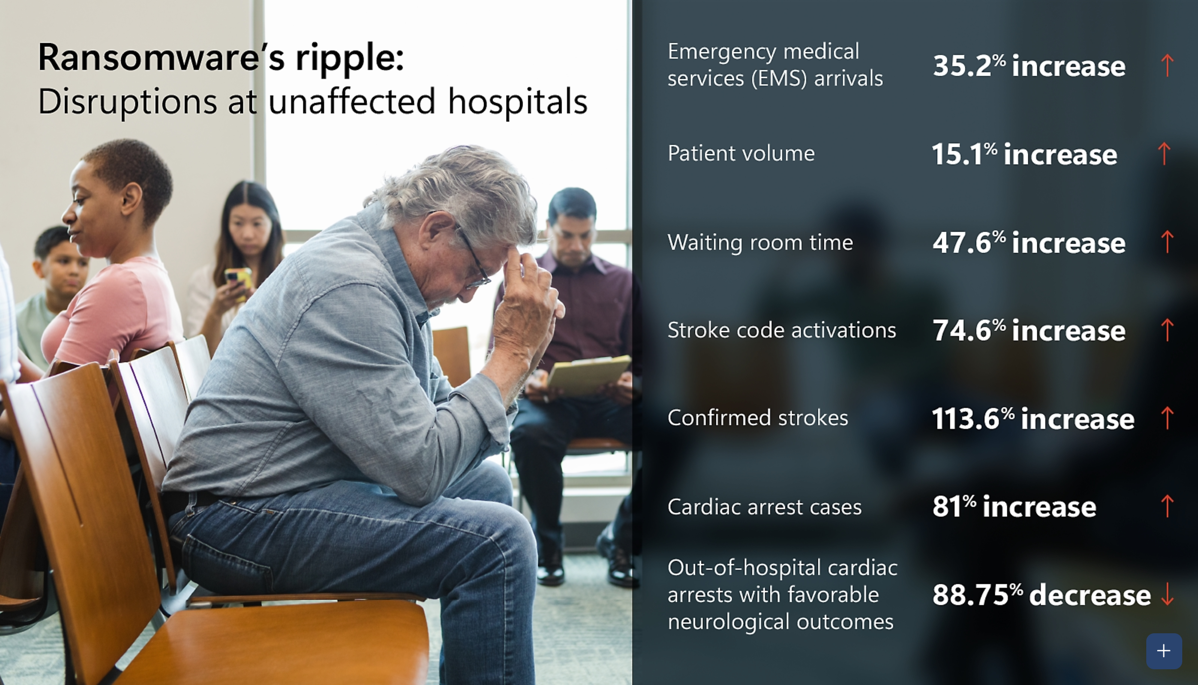
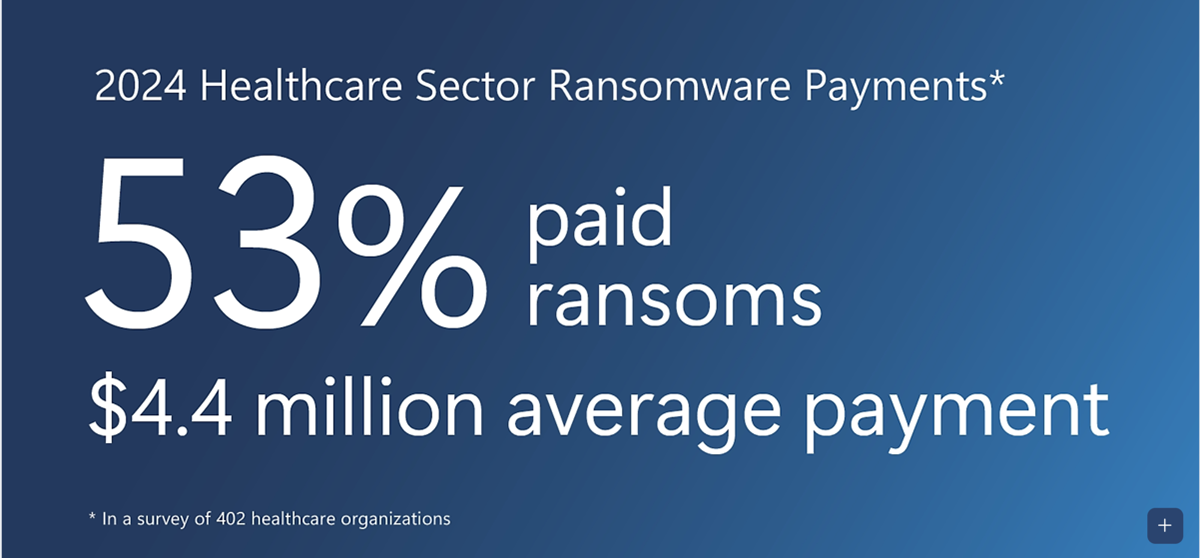
US Healthcare at Risk: Strengthening Resiliency Against Ransomware Attacks
The Ask: Create a focused, industry-specific report on the unique ransomware threats facing the healthcare sector, emphasizing the grave risk to patient care.
My Role: I synthesized threat intelligence data and expert interview transcripts into a detailed report, blending technical attack patterns (TTPs) with the real-world human impact.
The Outcome: A high-stakes industry report for Security Insider, giving healthcare CISOs actionable intelligence on protecting their organizations from life-threatening attacks.
Read feature story
Read feature story


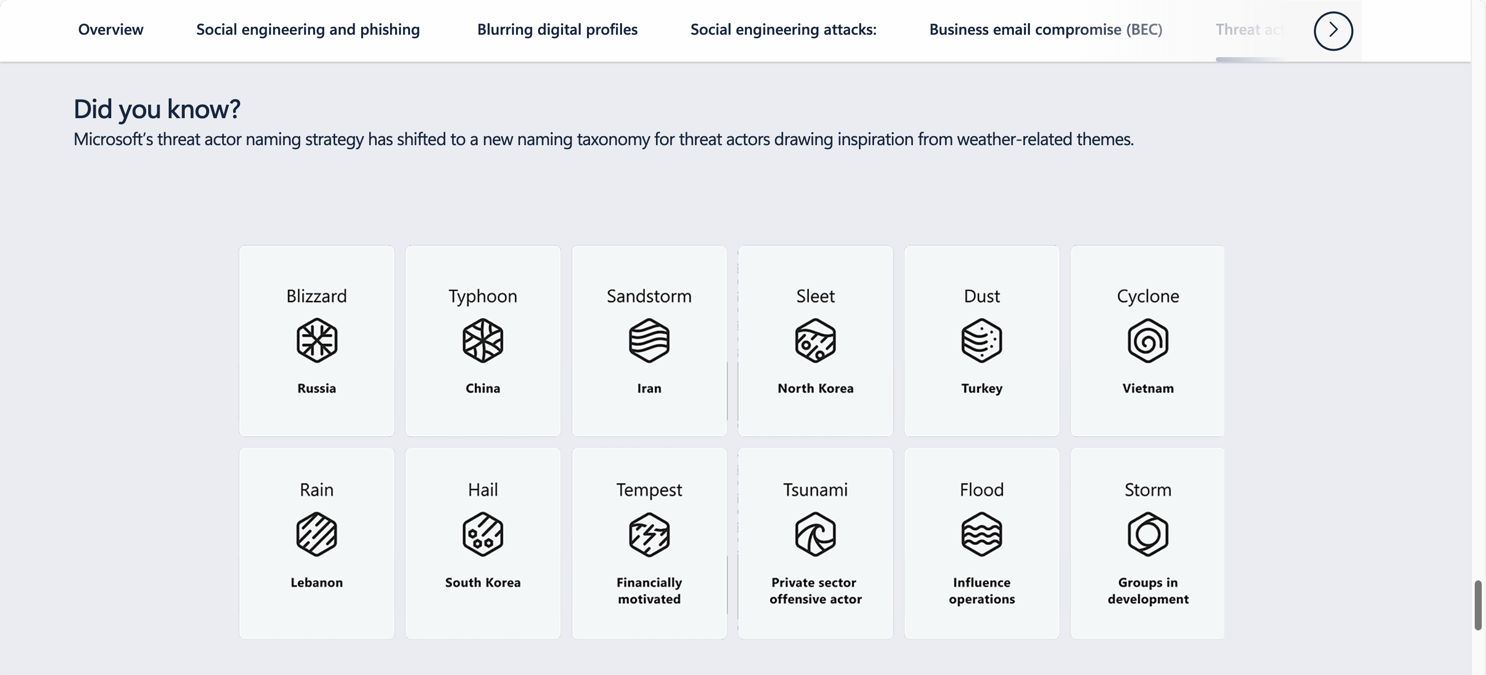
Bold Action Against Fraud: Disrupting Storm-1152
The Ask: Tell the complex, behind-the-scenes story of Microsoft's multi-year investigation and legal takedown of a major cybercrime-as-a-service operation.
My Role: I synthesized complex source material—including legal filings, technical reports, and multi-team interview transcripts—into a single, cohesive narrative about strategic threat disruption.
The Outcome: A feature story for Security Insider showcasing Microsoft's leadership through a unique blend of technical action and groundbreaking legal strategy.
Read feature story
Read feature story
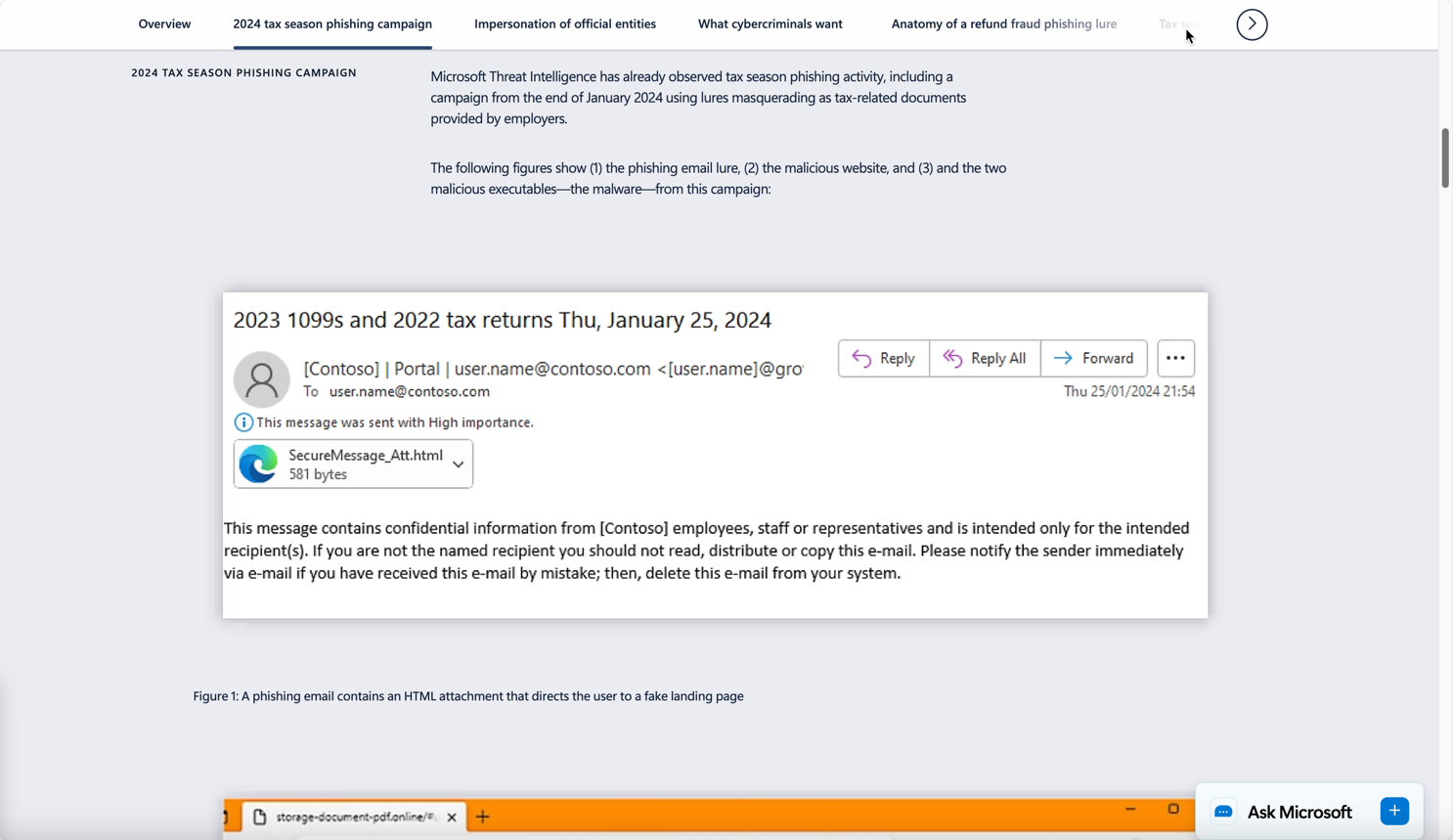
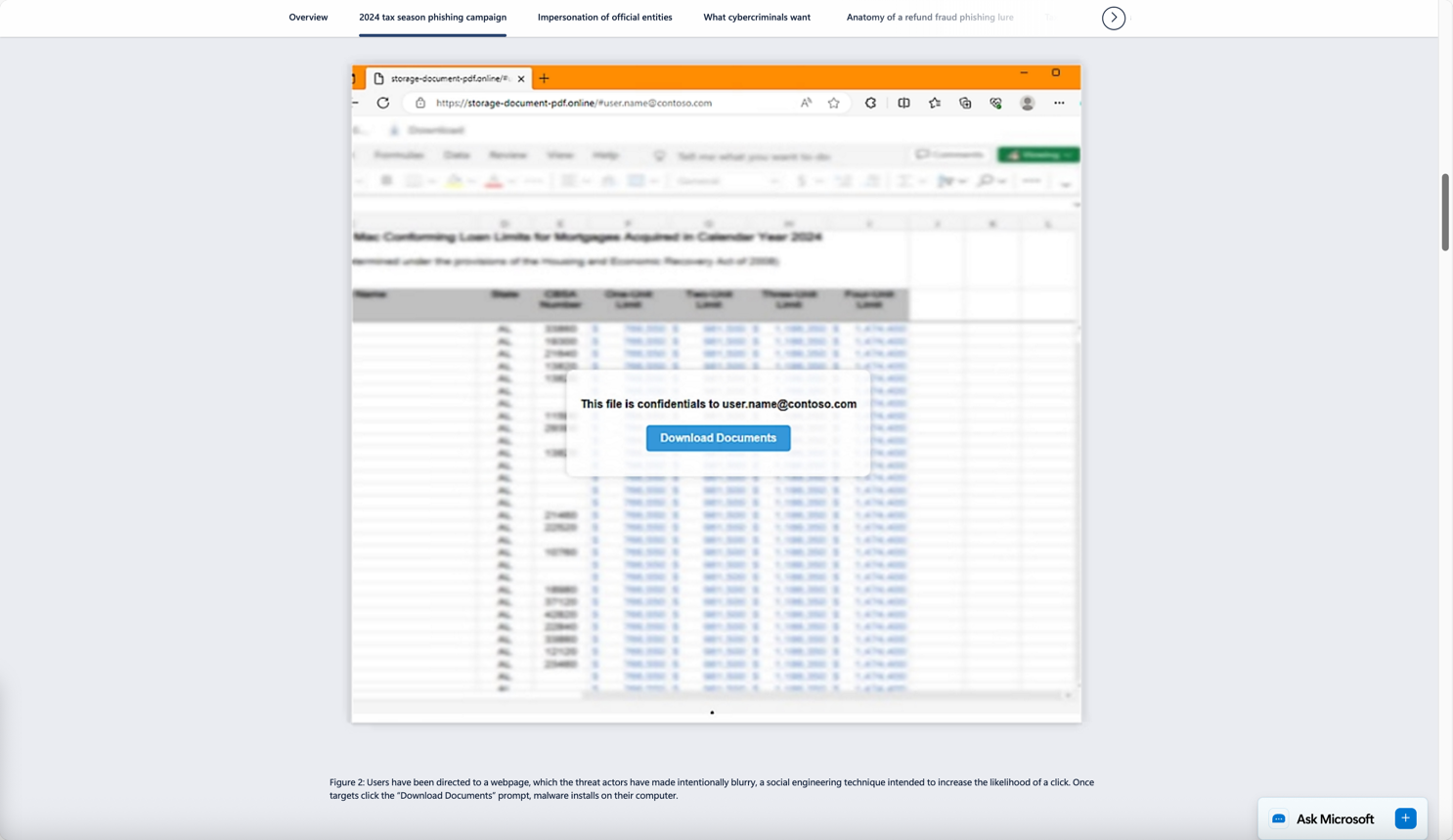
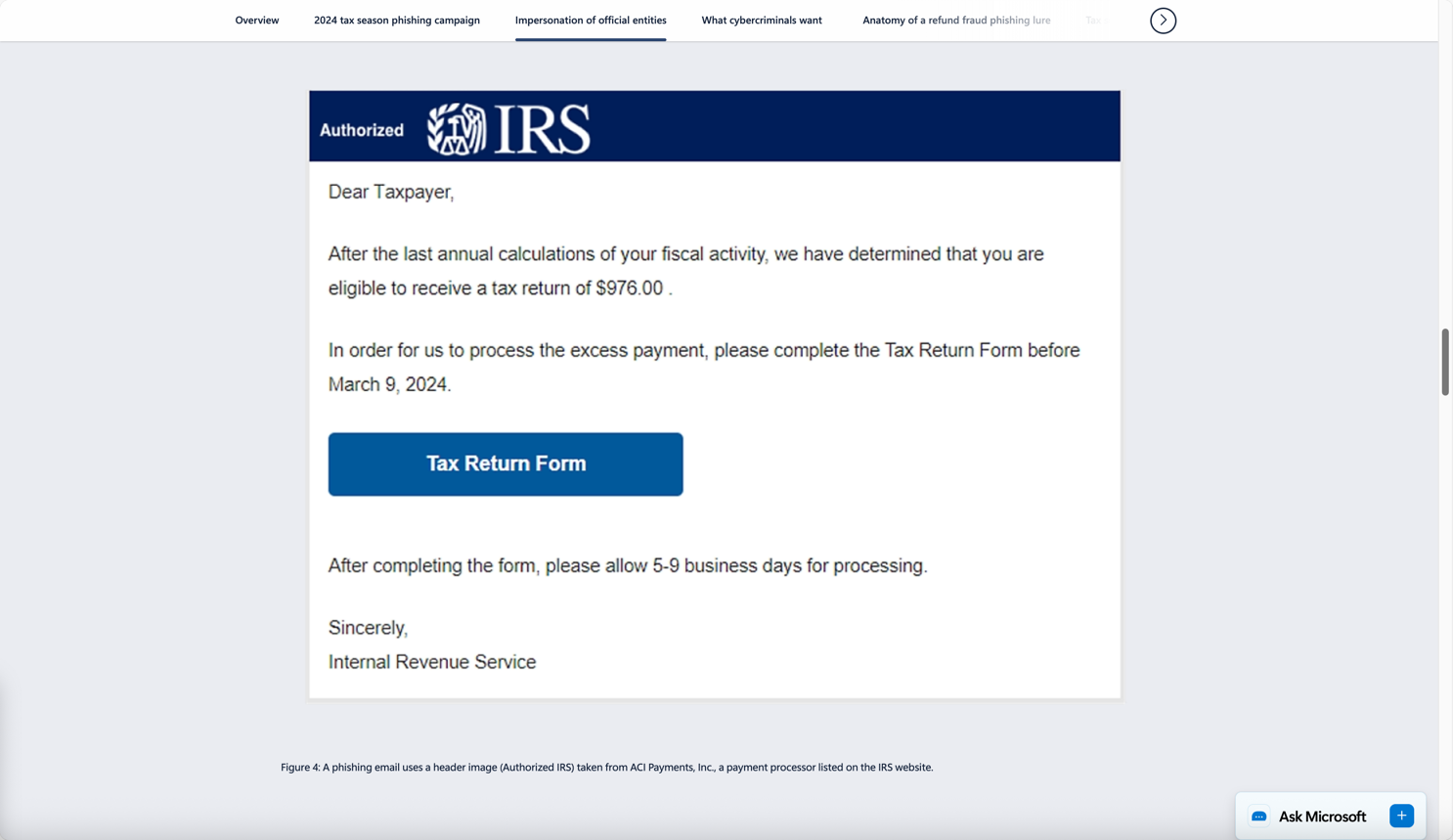
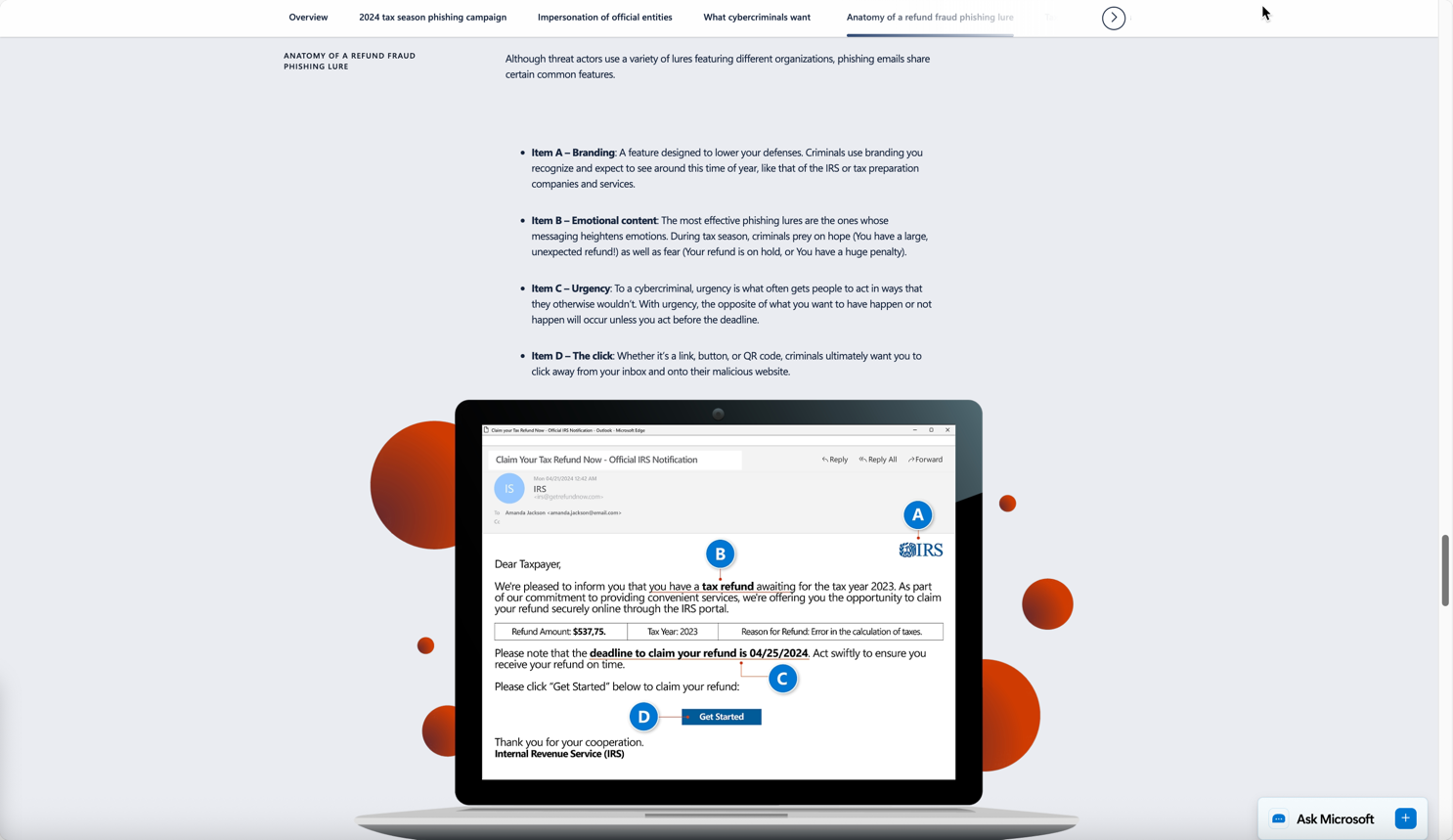
Tax Season Cybersecurity: What Cybercriminals Want and Who They Target Most. Is It You?
The Ask: Detail the specific cybercriminal tactics used during tax season and clearly identify who is most at risk, from individual filers to overworked accounting firms.
My Role: Based on SME kick-off call transcripts, I developed a practical guide illustrating the attack chain from social engineering to financial exploitation and identity theft.
The Outcome: A timely, seasonal article for Security Insider that provided actionable threat awareness for both a general business audience and targeted financial professionals.
Read feature story
Read feature story
Promotion & Amplification
I wanted an excuse to show the divorce agreement phish animation, but it's worth noting that I have written hundreds of social media posts promoting content I've written.